Meet the Man from Intrepid
A chance encounter with Ireland’s military intelligence led Neal O’Farrell down an encryption path that would put him into direct conflict with the NSA and a competition to build the world’s most secure, secure telephone.
Neal holds the slightly dubious distinction of being one of the first cybersecurity experts to be targeted and blacklisted by the US government because of his early work in encryption, and a year before the noted scientist and cryptographer Phil Zimmerman was very publicly targeted for the same reason.
Neal’s involvement in encryption goes back more than 40 years. It began in 1982 when straight out of the College of Marketing on Parnell Square, Neal was approached by a software startup looking for ways to protect their expensive new accounting software from being pirated.
The solution he found was a plug in “dongle” that used a type of encryption known as the Data Encryption Standard, or DES, and that’s where Neal’s obsession with encryption began. Ironically, a few years later Neal co-hosted with IBM one of Ireland’s first network security conferences, at UCD in Dublin in 1988. The keynote speaker was Dr. Carl Meyer, co-author of DES.
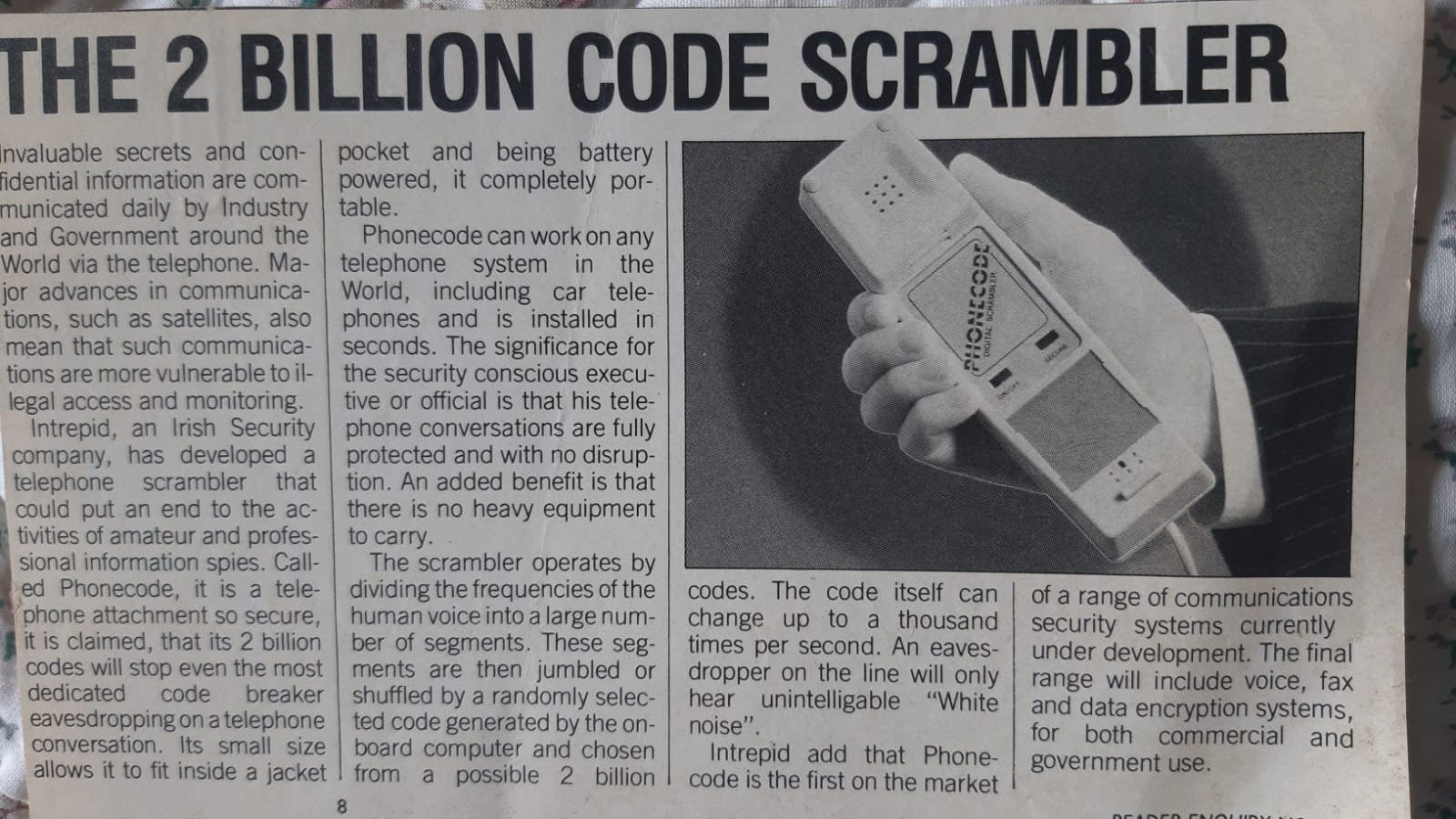
In 1986 and in response to a growing number of phone tapping scandals, Neal developed a telephone scrambler called PhoneCode to help the Irish government upgrade its aging secure telephones.
Not long after that and still in his twenties, the Irish Banks Standing Committee awarded Neal the first ever contract to encrypt Ireland’s national ATM network.
His big break came the same year when Neal was approached by the Irish Department of Defense Directorate of Signals Intelligence with an unusual request. The US National Security Agency had just released the latest version of the STU3 or STU-III, Secure Telephone Unit Generation 3, widely regarded as the most advanced and expensive secure telephone in the world.
The STU-III had been jointly developed by the NSA, AT&T, RCA, and Motorola, took more than a decade to develop, and at a cost believed to be more than $50 million.
Apart from being very expensive, at up to $6,000 per phone, the phone had numerous quality issues that made in unusable in many environments. But most important, the phone was widely rumored to have a back door that would allow the US government to listen into any conversations on the phone. Because the STU-III was used right up to presidential level, fears of a backdoor created significant security and political fears.
The Irish government was also suspicious of a recent offer by the US government to sell them a lower security version of the STU. The concern was that sensitive discussions. over Northern Ireland for example, might not be protected if that phone had a back door.
As a neutral country, Ireland had no restrictions on the development of advanced encryption systems and algorithms. And with Neal’s experience with both voice scrambling and data encryption, the Irish Defense Department hoped that Neal could blend those skills to come up with a better version of the STU-III. A safer, less expensive, less restrictive, and non-compromised European rival.
 Neal accepted the challenge, and the project and startup were named Intrepid.
Neal accepted the challenge, and the project and startup were named Intrepid.
The Baltimore Technologies Rivalry
Intrepid launched in 1989 and based itself in a small basement office on the east side of Fitzwilliam square. Less than 100 yards away was Ireland’s only other encryption startup, Baltimore Technologies.
In 1990 Baltimore’s founder Michael Purser approached Intrepid to either partner with us or license their technology. Intrepid had already developed something much superior but rather than basing it on the most common public key system, RSA, Intrepid had chosen an RSA competitor called the Diffie Hellman public key system.
The co-author of Diffie Hellman, Whitfield Diffie, was a legend in the world of cryptography and widely regarded as the grandfather of modern public key cryptography. Baltimore was also unaware that Whit Diffie was already on his way to Ireland to look at what Intrepid was working on.
There was a growing interest in encryption in Ireland amongst a number of leading entrepreneurs. Intrepid was backed and funded by the Irish government and the IDA, as well as a number of Irish entrepreneurs including Pat McDonagh of CBT and RiverDeep. McDonagh’s business partner Dermot Desmond later acquired Baltimore, who then sold it to Henry Beker, an advisor to Intrepid.
Henry Beker started his encryption career at Racal Comsec in Salisbury, UK, and Racal Comsec later became Intrepid’s first partner and customer. Stephen Farrell, Intrepid’s chief cryptographer, later became Director of Research for Baltimore.
The Launch of Milcode
Less than 18 months after that first conversation with the Department of Defense, Neal and his team of nearly 15 announced the arrival of what would eventually be called Milcode.
Milcode quickly won the crown as the world’s “most secure” secure telephone, and at the same time solving many of the technical and speech quality issues that had plagued the STU-III for years. In addition to encrypting speech, Milcode could also encrypt data and fax communications. And for as little as $1,500 per phone, it put truly secure communications within reach of a much bigger audience.
Neal and his team also developed Faxcode, the world’s first fully encrypting fax machine.
The End of Milcode
A live demonstration of Milcode was given to representatives of Plessey Crypto, a division of GEC Marconi, at the headquarters of the IDA in Wilton Place in mid 1990. At that meeting Plessey confirmed their interest and an estimated sales of at least 50 million pounds worth of Milcodes per year.
The feedback from Plessey was key to unlocking substantial long term funding from the IDA to bring the phone into production, but the IDA suddenly showed little interest and a later demonstration to Racal Comsec helped explain why. Racal had taken one of the phones to its headquarters in Salisbury so they could test the quality and performance of international calls between the UK and Intrepid’s office.
It was later revealed that those encrypted conversations were picked up by a global eavesdropping network known as Echelon, run by a group of five countries and surveillance partners known as the Five Eyes.
The inability of Echelon to crack the Intrepid code alerted the US to the existence of Milcode and triggered a series of events that would result in Intrepid and Milcode being blacklisted globally. It was alleged that if Milcode became widely available, and capable to encrypting voice, data, and fax communications to an unbreakable level, it would pose a major threat to the eavesdropping capabilities of Echelon.
Not long after that, in early 1991, and while still in discussions with Intrepid and still a part owner, the IDA announced funding of £3 million for a US manufacturer of a rival secure telephone to set up a production facility in Blanchardstown. The company was called Cylink, their secure phone was vastly inferior to Milcode, and in spite of public pressure the IDA refused to explain why they chose to fund Cylink over Intrepid. The Cylink factory never opened.
After a short campaign of bomb threats, break-ins, and blacklisting, Intrepid finally folded in 1991. Like a number of other encryption startups, Intrepid became victim of the Crypto Wars and efforts by the US government to stifle any efforts to make unbreakable encryption widely available.
Until the mid 1990s encryption was listed by the US government as a weapon and licensed as such. Any attempt to circumvent strict weapons exporting and licensing laws were quickly dealt with. For example, the same year that Intrepid closed, noted scientist and cryptographer Phil Zimmerman, the creator of the free PGP encryption program, was arrested by the FBI and investigated for five years for trying to make unbreakable encryption available to the public.
Those restrictions were finally lifted in 1996 by an executive order signed by President Bill Clinton.
Neal later moved to London where he worked with GCHQ on the development of a new secure telephone based on the Clipper/Skipjack encryption system. The Clipper chipset had also been developed by the NSA but was later abandoned for a number of reasons including known security weaknesses and concerns over a deliberate backdoor that could allow for warrantless government surveillance.